Sample Exams (Type of Attack, Hat)
Sample Exams of Cybersecurity
In these series we have some “Sample Exams of Cybersecurity”, “Practice Cybersecurity Examinations”, “Cybersecurity Test Previews” and “Mock Cybersecurity Tests”
Type of Attack:
1. Hacktivists:
These are individuals or groups who engage in hacking activities to promote a social or political agenda. Their goal is to raise awareness or effect change through their actions.
2. Cybercriminals:
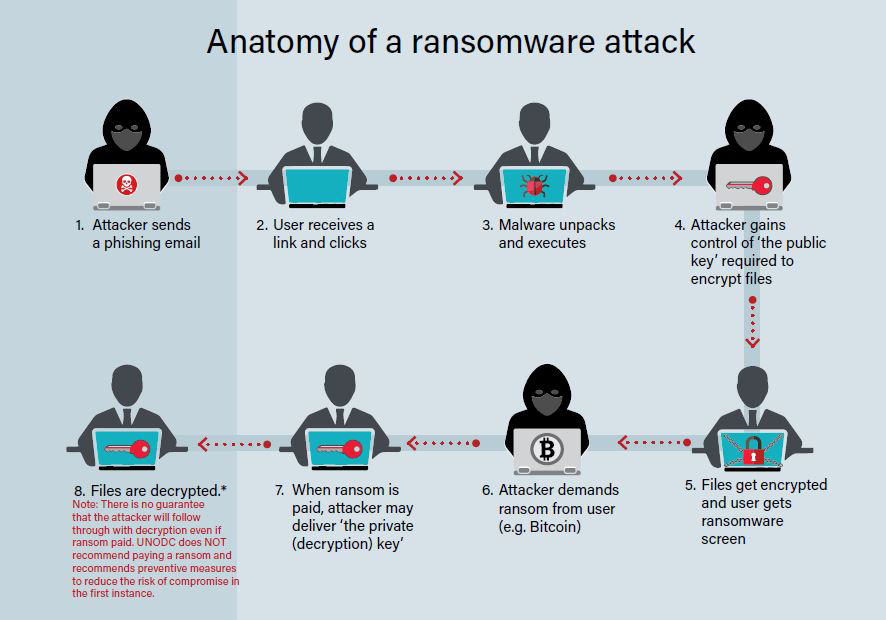
Cybercriminals are motivated by financial gain. They may engage in activities like stealing personal information, credit card data, or conducting ransomware attacks to demand money from victims.
3. Nation-State Actors:
Governments and state-sponsored groups conduct cyber-espionage and cyber-attacks to gain a competitive advantage, steal sensitive information, or disrupt the infrastructure of other nations.
4. Insiders:
Insiders are individuals within an organization who misuse their authorized access to commit cybercrimes. They can be current or former employees, contractors, or business partners.
5. Script Kiddies:
These are individuals with limited technical skills who use pre-written scripts or tools to launch attacks. They often do it for the thrill rather than any specific goal.
6. Organized Crime Groups:
Some cybercriminals operate as part of organized crime networks. They may engage in activities like credit card fraud, identity theft, or cyber-extortion.
7. Phishers:
Phishers use social engineering techniques to trick individuals into revealing sensitive information, such as usernames, passwords, and financial data. They often send fraudulent emails or messages that are from legitimate sources.
8. Malware Authors:
Individuals who create and distribute malicious software, such as viruses, Trojans, and ransomware. Their goal is to infect computers and steal data or disrupt operations.
9. Advanced Persistent Threat (APT) Actors:
APT groups are typically nation-state or highly skilled attackers who use sophisticated, long-term attacks to infiltrate and maintain access to a target network. Their primary goals are espionage or data theft.
10. Hackers for Hire:
These are individuals or groups that offer hacking services to the highest bidder. They can be hired for various purposes, including corporate espionage, data theft, or taking down websites.
11. Data Brokers:
Data brokers gather, compile, and sell personal information and data obtained from various sources. While not directly engaging in hacking, their activities can indirectly support cybercrime by providing stolen data to other attackers.
12. Extortionists:
Extortionists threaten to expose sensitive information or launch attacks on a target unless a ransom is paid. Ransomware attacks are a common method used by extortionists.
13. Cybersecurity Researchers (Ethical Hackers):
While not attackers in the malicious sense, ethical hackers, or white hat hackers, actively seek vulnerabilities in systems and networks to help organizations strengthen their security.
14. Unintentional Threats:
Sometimes, individuals may inadvertently pose a security threat through their actions, such as falling victim to phishing attacks or using weak passwords. They are not malicious attackers but can inadvertently compromise security.
What Color Is My Hat of Attackers on cyber security?
White Hat:
White hat hackers are ethical hackers who work to identify and fix security vulnerabilities in systems. They are often employed by organizations to conduct penetration testing and security assessments to improve security.
Black Hat:
Black hat hackers are malicious hackers who engage in cybercriminal activities, such as hacking for financial gain, stealing sensitive data, or causing harm to computer systems and networks.
Gray Hat:
Gray hat hackers fall somewhere in between white hat and black hat hackers. They may discover and disclose security vulnerabilities without authorization but without malicious intent. However, their actions may still be legally questionable.
Red Team:
A red team is a group of skilled professionals who simulate cyberattacks to test the security of an organization’s systems. They can be either internal or external to the organization.
Blue Team:
Blue team refers to the defenders of a network or system. They work to prevent and mitigate cyberattacks and respond to security incidents.
You can find other learning for Security by clicking here.